[Show abstract] [Hide abstract] ABSTRACT: This document describes the Enhanced Link Condition Routing (OLSR) protocol for mobile random systems. The protocol is definitely an optimization from the classical link condition formula tailored towards the needs of the mobile wireless LAN. The important thing concept utilized in the protocol is multipoint relays (MPRs). MPRs are selected nodes which forward broadcast messages throughout the flooding process. This method substantially cuts down on the message overhead when compared with a flooding mechanism, where every node retransmits each message if this has got the first copy from the message. In OLSR, link condition details are generated only by nodes elected as MPRs. Thus, another optimization is achieved by minimizing the amount of control messages flooded within the network. Like a third optimization, an MPR node may made a decision to report only links between itself and it is MPR selectors. Hence, as resistant to the classic link condition formula, partial link condition details are distributed within the network. This post is then employed for route calculation. OLSR provides optimal routes (when it comes to quantity of hops). The protocol is especially appropriate for big and dense systems as the method of MPRs is effective within this context.
Full-text · Article · Jan 2003 · IEEE Wireless Communications
Thomas Clausen Philippe Jacquet
[Show abstract] [Hide abstract] ABSTRACT: An advertisement hoc network is an accumulation of wireless computers (nodes), communicating among themselves over possibly multihop pathways, without the assistance of any infrastructure for example base stations or access points. Although a lot of previous random network routing protocols happen to be located in part on distance vector approaches, they’ve generally assumed a reliable atmosphere.
Within this paper, we design and assess the Secure Efficient Random Distance vector routing protocol (SEAD), a safe and secure random network routing protocol in line with the style of the Destination-Sequenced Distance-Vector routing protocol. To be able to support use with nodes of limited CPU processing capacity, and also to guard against Denial-of-Service attacks by which an assailant tries to cause other nodes to eat excess network bandwidth or processing time, we use efficient one-way hash functions and don’t use uneven cryptographic operations within the protocol. SEAD performs more than the plethora of scenarios we tested, and it is robust against multiple uncoordinated attackers creating incorrect routing condition in almost any other node, even regardless of any active attackers or compromised nodes within the network.
Article · November 2003
Yih-Chun Hu David B. Manley Adrian Perrig
[Show abstract] [Hide abstract] ABSTRACT: Lately, mobile random systems grew to become a warm research subject among researchers because of their versatility and independence of network infrastructures, for example base stations. Because of unique characteristics, for example dynamic network topology, limited bandwidth, and limited electric batteries, routing inside a MANET is an especially challenging task over a conventional network. Early operate in MANET studies have mainly centered on developing a competent routing mechanism in this highly dynamic and resource-restricted network.
At the moment, several efficient routing protocols happen to be suggested for MANET. Many of these protocols assume a reliable and cooperative atmosphere. However, in the existence of malicious nodes, the systems are susceptible to several types of attacks. In MANET, routing attacks are particularly serious. In the following paragraphs, we investigate condition-of-the-art of security issues in MANET. Particularly, we examine routing attacks, for example link spoofing and colluding misrelay attacks, in addition to countermeasures against such attacks in existing MANET protocols.
Article · November 2007




 Dissertation proposal sample management resume
Dissertation proposal sample management resume University of the philippines computer science thesis proposal title
University of the philippines computer science thesis proposal title Niasa architecture thesis proposal titles
Niasa architecture thesis proposal titles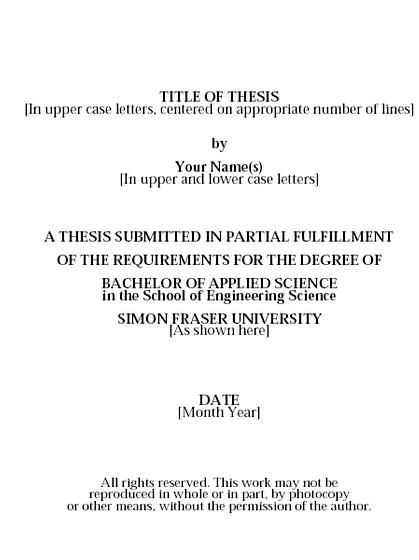 Sample title page masters thesis proposal
Sample title page masters thesis proposal Master thesis proposal computer science
Master thesis proposal computer science